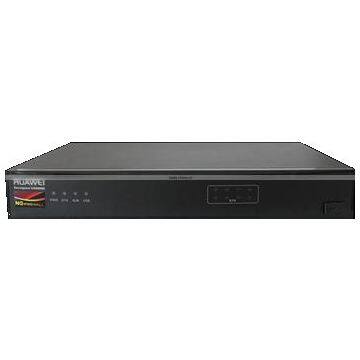
Huawei USG6320-BDL-AC NGFW AC
USG6320 AC Host(8GE(RJ45),2GB Memory,with IPS-AV-URL Function Group Update Service Subscribe 12 Months)
- Desktop Type, 8GE(RJ45),
- 2Gbps throughput(FW+APP)
- Default 10 vSys and 100 SSL users
- Support Applications awareness, IPS, Anti-Virus, URL filter, DLP, Anti-DDoS, Anti-Spam, IPSec VPN, SSL VPN and Virtualization features etc.
Features
Granular Application Access Control
- Identifies the application-layer attacks and their application, content, time, user, and location information.
- Provides all-round visibility into service status, network environment, security postures, and user behaviors.
- Provides an analysis engine that integrates application identification and security functions, such as IPS, AV, and data leak prevention, to prevent application-based malicious code injections, network intrusions, data interceptions, and Advanced Persistent Threat (APT) attacks.
Easy Security Management
- Classifies 6000+ applications into 5 categories and 33 subcategories and supports application access control based on the subcategories.
- Complies with the minimum permission control principle and automatically generates policy tuning suggestions based on network traffic and application risks.
- Analyzes the policy matching ratio and discovers redundant and invalid policies to remove policies and simplify policy management.
Excellent Performance
- Provides an Intelligent Aware Engine (IAE) capable of parallel processing with all security functions enabled after intelligent application identification.
- Improves application-layer protection efficiency and ensures the 10G+ performance with all security functions enabled.
Prevention of Unknown Threats
- Provide samples of worldwide suspicious threats. Executing suspicious samples within the sandbox in the cloud to monitor the activities of the samples and identifies unknown threats.
- Automatically extracts threat signatures and rapidly synchronizes the signatures to the devices to defend against zero-day attacks.
- Prevent Advanced Persistent Threat (APT) attacks using a reputation system.
Specifications
| Model | USG6310 | USG6320 |
|---|---|---|
| Firewall throughput | 1 Gbit/s | 2 Gbit/s |
| IPS throughput | 300Mbit/s | 700Mbit/s |
| IPS+AV throughput | 300Mbit/s | 700Mbit/s |
| Concurrent sessions | 300,000 | 500,000 |
| New sessions per second | 10,000 | 20,000 |
| VPN Throughput (IPSec, 3DES) | 300Mbit/s | 400Mbit/s |
| Virtual firewalls | 20 | 20 |
| Fixed port | 8GE | |
| Expansion Slots | - | |
| Interface module | - | |
| Height | Desktop(Can be installed in rack) | |
| Dimensions (H x W x D) | 300*220*44.5 | |
| Weight (full configuration) | 1.7kg | |
| HDD | - | |
| Redundant power supply | - | |
| AC power supply | 100 V to 240 V | |
| DC power supply | - | |
| Maximum power | 60W | |
| Operating environment: (Temperature/ Humidity) |
Temperature: 0℃ to 40℃ Humidity: 10% to 90% |
|
| Non-operating environment | Temperature: -40℃ to 70℃/Humidity: 5% to 95% | |
| Functions | |
|---|---|
| Context awareness | ACTUAL (Application, Content, Time, User, Attack, Location)–based awareness capabilities |
| Eight authentication methods (local, RADIUS, HWTACACS, SecureID, AD, CA, LDAP, and Endpoint Security) | |
| Application security | Fine-grained identification of over 6000 application protocols, application-specific action, and online update of protocol databases |
| Combination of application identification and virus scanning to recognize the viruses (more than 5 millions), Trojan horses, and malware hidden in applications | |
| Combination of application identification and content detection to identify file types and sensitive information to prevent information leaks | |
| Intrusion prevention | Provides over 5000 signatures for attack identification. |
| Provides protocol identification to defend against abnormal protocol behaviors. | |
| Supports user-defined IPS signatures. | |
| Web security | Cloud-based URL filtering with a URL category database that contains over 85 million URLs in over 80 categories |
| Defense against web application attacks, such as cross-site scripting and SQL injection attacks | |
| HTTP/HTTPS/FTP-based content awareness to defend against web viruses | |
| URL blacklist and whitelist and keyword filtering | |
| Email security | Real-time anti-spam to detect and filter out phishing emails |
| Local whitelist and blacklist, remote real-time blacklist, content filtering, keyword filtering, and mail filtering by attachment type, size, and quantity | |
| Virus scanning and notification for POP3/SMTP/IMAP email attachments | |
| Data security | Data leak prevention based on content awareness |
| File reassembly and data filtering for more than 30 file types (including Word, Excel, PPT, and PDF), and file blocking for more than 120 file types | |
| Security virtualization | Virtualization of security features, forwarding statistics, users, management operations, views, and resources (such as bandwidths and sessions) |
| Network security | Defense against more than 10 types of DDoS attacks, such as the SYN flood and UDP flood attacks |
| VPN technologies: IPSec VPN, SSL VPN, L2TP VPN, MPLS VPN, and GRE | |
| Routing | IPv4: static routing, RIP, OSPF, BGP, and IS-IS IPv6: RIPng, OSPFv3, BGP4+, IPv6 IS-IS, IPv6 RD, and ACL6 |
| Working mode and availability | Transparent, routing, or hybrid working mode and high availability (HA), including the Active/Active and Active/Standby mode |
| Intelligent management | Evaluates the network risks based on the passed traffic and intelligently generates policies based on the evaluation to automatically optimize security policies. Supports policy matching ratio analysis and the detection of conflict and redundant policies to remove them, simplifying policy management. |
| Provides a global configuration view and integrated policy management. The configurations can be completed in one page. | |
| Provides visualized and multi-dimensional report display by user, application, content, time, traffic, threat, and URL. | |

Send Inquiry to This Supplier
You May Also Like
-
ALLINGE MDZ3233 WE1626 Router Support USB Modem With 4 External Antennas 802.11g 300Mbps Openwrt Wireless WiFi RouterNegotiableMOQ: 1
-
Huawei CR5D0L5XFA70 03030PMC P51-5x10GBase LAN/WAN-SFP+-A LPUF-51 5-Port 10GBase LAN/WAN-SFP+ P51-A for Huawei NE40E NE80EUS$ 1 - 50MOQ: 1 Piece
-
Network Hardware Platforms Appliance With Motherboard Based on a Range of Processors From Intel® Atom™, Intel® Core™, Xeon for Your ProjectNegotiableMOQ: 1 Piece
-
Industrial 5-port 4G Card Router, Industrial Wifi Module, Video Surveillance Electric Pile CPE Internet Access MR500UNegotiableMOQ: 1 Combo
-
ISR4321/K9 ISR 4321. (2GE,2NIM,4G FLASH,4G DRAM,IPB). New Sealed Cissco RouterNegotiableMOQ: 1 Piece
-
Main Treatment Board 02353354 03050AXP ES0Z1B06ACS0 03050DEP ME0D0SRUAH70 IG2D0SRUAD02NegotiableMOQ: 1 Piece
-
Plery R602 2.4GHz 300Mbps Unlocked 4G Wifi Hotspot Routers Wifi6 Internet SIM Card Router for RuralUS$ 13.9 - 19.9MOQ: 5 Pieces
-
SA NSA Waterproof IP 65 Outdoor 5g RouterUS$ 220 - 260MOQ: 1 Piece
-
NetPower 16P CRS318-16P-2S+OUT Outdoor SwitchNegotiableMOQ: 1 Piece
-
MT7628 Industry Wireless Sim Card Routers 150Mbps Cat4 4G LTE CPE 2.4Ghz Wifi 1 Wan 1 Lan 2Port Mini 3G 4G Industrial M2M RouterUS$ 55 - 60MOQ: 1 Piece